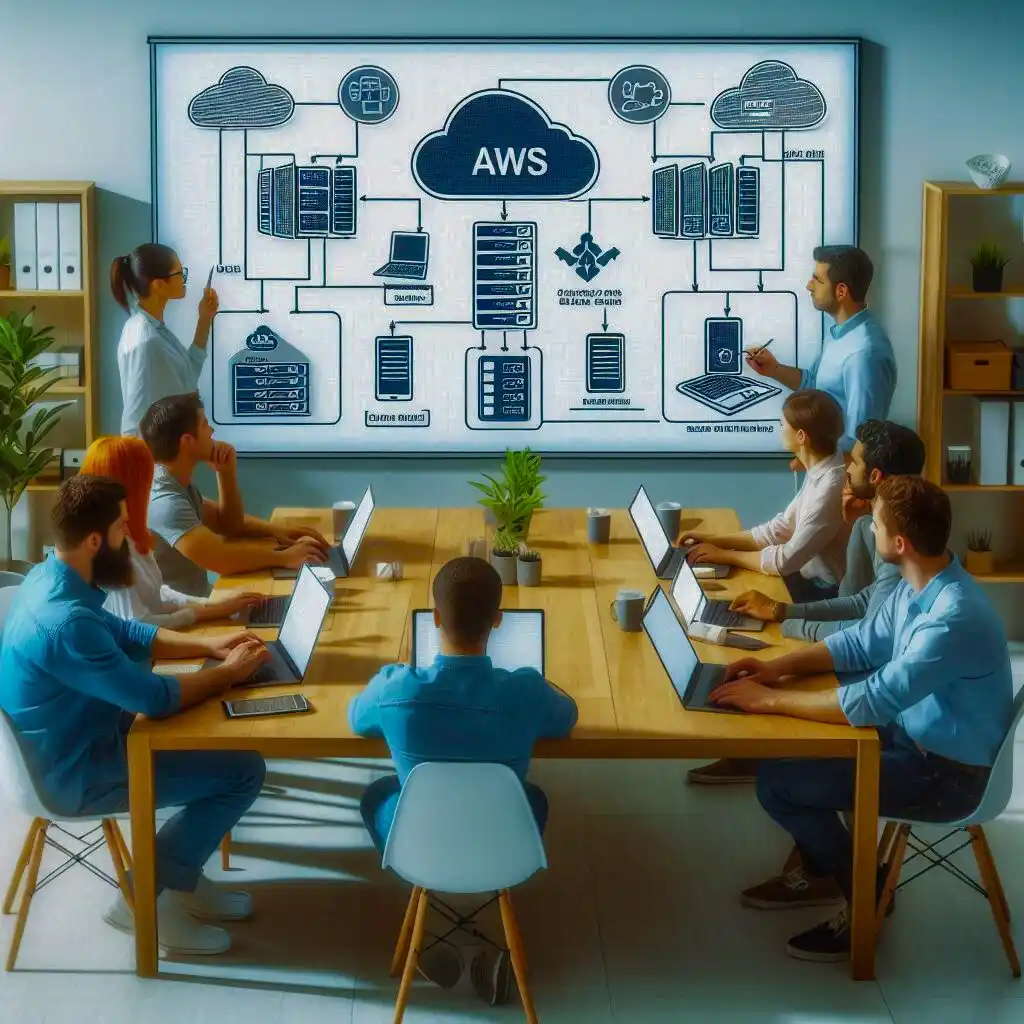
AWS Configuration Review & Audit Services In UAE
Get Actionable Insights to Secure your AWS Infrastructure
What is AWS Security Configuration Review Services?
An AWS Configuration review is an in-depth assessment of your Amazon Web Services infrastructure, conducted to identify vulnerabilities due to improper configurations or not following best practices. It is an essential test that not only facilitates protection of your AWS environment from potential cyberthreats, it also enables you to maintain regulatory compliance.
The Wattlecorp team can perform this evaluation swiftly and efficiently. Our team verifies whether the security controls are properly implemented and updated. AWS Configuration review is especially important for those businesses that handle sensitive information or belong to industries with stringent regulations. AWS configuration audits are geared towards evaluating and enhancing your AWS environment’s structural security aspects, with special focus on critical components like Amazon EC2,Amazon S3, Amazon RDS, Amazon VPC, Amazon DynamoDB, Amazon ECS, AWS IAM, and Amazon EKS.

Benefits of Conducting AWS Configuration Review & Audit
Our AWS configuration review services help you understand how secure your AWS environment is, what vulnerabilities are present, and the potential impact of breaches. We provide a detailed report of our findings that can benefit you in numerous ways.
Maintain compliance with various regulations, ensure you implement adequate security controls and logging to mitigate cyberattacks, and make sure that your AWS cloud infrastructure is robust enough to withstand attacks, improving your overall security posture.
Reconnaissance
We gather information on your network, users, cloud configurations, and understand the needs and goals of your business.
Review
We evaluate your Google cloud platform thoroughly to detect security gaps and vulnerabilities in your GCP environment using a combination of manual and automated tools.
Reporting and remediation
Our team provides a detailed report of our review and makes recommendations to implement best practices and bridge security gaps.
Recheck
After applying the remedial measures, we conduct another assessment to verify that all issues have been addressed and that risk is mitigated.
Listen to People
We help companies to protect their online assets.
Checkout our Services
F.A.Q
We have something for everyone, including pricing and answers.
Tip • Book a consultation to get personalised recommendations.
Start Your AWS Configuration Review & Audit Services Now !
All you need to do is fill the form below.
Recommended Services
Officially recommended by Hackers.
Wireless Penetration testing
Uncover hidden vulnerabilities in your wireless network with our expert Wireless Penetration Testing services.
ICS / SCADA Security
Safeguard your industrial control systems from cyber threats.
Managed Threat Hunting
Proactively identify and neutralize threats before they cause damage.
Pro Active Threat Hunting
Uncover and neutralize hidden threats before they cause damage.
Recent Articles
stay up to date with recent news.

NOTPETYA MALWARE: Cyber World’s Foe

Brute Force Attacks
Skills Required To Become A Hacker : Skills You Can’t Ignore

The Role of Penetration Testers in the Era Of Vulnerability Scanners
Mobile App Security Best Practices In 2025

Cybersecurity for Small Businesses: Essential Strategies for Limited Resources

Top 15 Cybersecurity Frameworks in 2024

Why Penetration Testing is Essential for Secure API Development

Top 5 Security Challenges Faced by SaaS Products [And How to Avoid Them]
How to Stay Updated with Latest Cybersecurity News & Events

Different Types Of Hackers: A Comprehensive Guide (2024)

2024 HIPAA Compliance Checklist: Enhancing Healthcare Cybersecurity

Top 10 Hacking Apps & Tools On Android 2024

VAPT Cost in UAE: What to Expect and Why It’s Worth It

Key Cybersecurity Threats Addressed By VAPT In 2025

Tips To Improve Security Of Android Smartphones (2024)

Debunking Common Cyber Security Myths: Unveiling the Reality

Annual VAPT Checklist for Secure Business Operations in UAE

Best Practices for Achieving DORA Compliance: Strengthening Cybersecurity in Financial Services

Large Language Model (LLM) Security: Risks, Checklists & Best Practices
Critical Vulnerabilities In Microsoft Windows Codec Library: Stay Informed

IoT Security Risks and Best Practices for Securing Your IoT Devices
The Importance of Penetration Testing in 2024

